Cyber Security For Employees
- Product ID
- tabccemp_vod
- Training Time ?
- 16 to 26 minutes
- Language(s)
- English,Spanish
- Video Format
- High Definition
- Required Plugins
- None
- Number of Lessons
- 10
- Quiz Questions
- 10
- Question Feedback
- Wrong Answer Remediation
- Lesson Bookmarking
- Downloadable Resources

Cyber Security For Employees
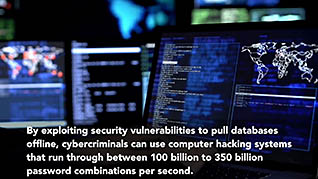
The damage of a successful cyberattack can be catastrophic. Money, time, productivity, reputation, brand identity and investor confidence are just a few of the negative consequences of a breach. This video highlights the importance of protecting data, and what an employee’s role is in data protection. Most data breaches occur because of human error.
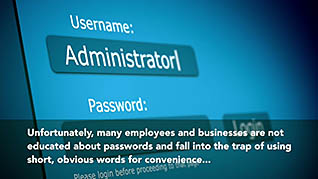
Computer passwords, network passwords, and knowing the risks in certain emails can be what protects important information on a computer or a server. Hackers have become advanced by using social engineering. This way they can phish information from a person by posing as someone else. This course shows employees what to look out for in their email, how to create strong passwords, and what other best practices they should following when sharing information and using their computer.
Changing passwords, locking one’s computer, and watching for red flags when sharing information, can all be what makes the difference in information remaining secure. Use this course to help employees learn to avoid being the weak link in the organization’s network.
![]() This course is in the Video On Demand format, to read about Video On Demand features click here.
This course is in the Video On Demand format, to read about Video On Demand features click here.
- Full-screen video presentation
- Print certificate and wallet card
- You have 30 days to complete the course
All employees
- Introduction
- Passwords
- Security Updates
- Public Network Connections
- Home Network Connections
- USB Drives
- Websites
- Other Security Risks
- Conclusion
© Mastery Technologies, Inc.